About Customer
The customer is a major NBFC having a wide presence across 36 countries in Asia, North America, Latin America, and Africa, with an end-user base of over 30 million. Through their joint ventures and subsidiaries, they cater to a diverse range of end-user needs.
The Need for Secure Infrastructure to Go Digital
With an aim of embracing digital transformation to provide its end-users a great, new edge experience, the customer wanted to secure their existing cloud environment first. They were looking for the right consulting, assessment, and implementation of security for their platform, web application, and data. Protecting their users’ data within various solution components was a top priority.
The existing cloud environment of the customer was in the need of security review and assessment. It lacked many advanced features in security services and the AWS organization-specific structure. Moreover, identifying security incidents was a critical challenge.
Blazeclan’s Security Consulting and Implementation
After understanding the customer requirements, Blazeclan’s team of certified cloud and security experts proposed a multi-fold approach to help the customer achieve its objectives and desired outcomes. Following approach was followed for meeting the customer’s requirements.
- Conducted security assessment reviews and gap analysis to study their existing environment.
- Custom AWS CloudFormation scripts were leveraged for environment hardening and ensuring that security best practices are followed in the cloud environment.
- After hardening their account from network security perspective, the cloud perimeter security was activated. Also, a web application firewall was installed to protect their web application.
- Considering security as part of the workflow, automated threat detection, vulnerability management, and incident response, the deployment process was accelerated by using Blazeclan’s cloud security automation framework.
- CIS benchmarks were enforced using automated scripts, which set and ensured the baseline controls for security.
- The management plane was separated from the data plane by incorporating the multi-account strategy. This also separated the security and management resources from the production resources.
- The VPC was reconfigured for creating subnets and CIDRs, which allowed the customer to setup a VPN connection from their corporate office to AWS cloud to data protection.
- The data stored in Amazon S3, Amazon EBS, and Amazon RDS was encrypted.
- To better control the network and user traffic, proxy server/load balancer was setup, which acted as a network traffic filter abreast VPC NACLs and security groups. This added an extra layer of security at the network level.
- A highly resilient infrastructure was achieved through a DR site setup to eliminate challenges associated with latency and compliance.
Benefits Achieved by the Customer
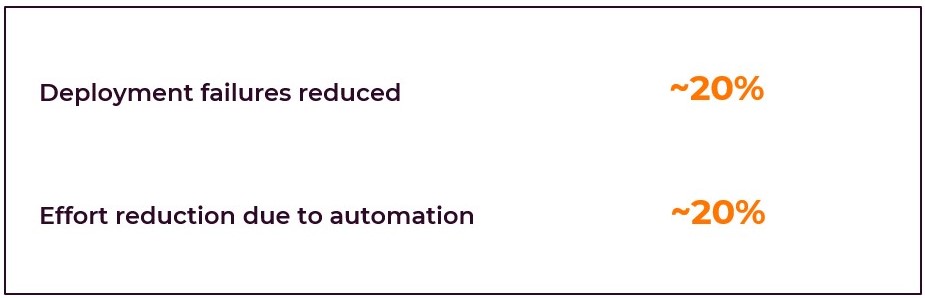
- Updating the security infrastructure design into a segregated environment with the right service configurations resulted in a highly reliable security setup along with the capability to scale vis-à-vis security issues.
- Adoption of AWS native security service improved the security posture of the customer’s environment, particularly for automated deployment and new infrastructure setup.
- Employing automation ensured complete visibility into the security posture of the cloud environment, without any significant rise in cost of consumption.
Tech Stack
| Amazon CloudWatch | Amazon CloudTrail | Amazon ElastiCache |
| Amazon API Gateway | AWS KMS | NAT Gateway |
| Amazon GuardDuty | AWS WAF | AWS CloudFormation |
| Amazon EBS | Amazon S3 | Amazon RDS |
| Amazon VPC | Outbound Proxy |